Identity Providers – Twitter
Federated identity seems to have sneaked up on us. A couple of years back federated identity was some huge enterprisey thing that was costly and took time to implement. Then a bunch of service providers started to be identity providers, but there were no relying parties making the whole effort somewhat useless. Now it seems that the relying parties have come. I’m going to start by taking a look at Twitter, and the sites that use it.
The user experience
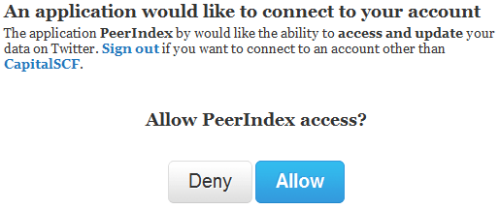
I for one am sick of having to create a new account for every website I want to interact with, so it’s great when I can just click a button instead:
On first use there’s a splash screen asking if it’s OK for the web site (relying party) to interact with Twitter (identity provider) on behalf of that user, and that’s it, we’re done. Provided that you’re signed into Twitter using a browser you can get straight into the site in future.
We are what we Tweet
Using a Twitter identity to sign in to Twitter related sites makes perfect sense. There’s just no reason why users of that type of site wouldn’t already have a Twitter account to reuse, so for things like PeerIndex it’s perfect.
There is of course the anti-pattern of firstly getting people to sign in with Twitter, and then asking them to provide a password (for a presumably standalone account) – PlanCa.st – I’m looking at you (this is one user that you lost to identity management failure).
For sites that don’t revolve around Twitter it’s still nice to have the option not to create a new identity, and of course Twitter can sit alongside of other providers when that makes sense.
Persona
Having multiple Twitter identities seems to be something that’s broadly accepted. Certainly tools like TweetDeck make it easy to maintain several personae. Things get a bit tricky in the browser though, as you can only be signed into one identity per browser; though this is where ‘porn mode’ can come to the rescue by providing a cookie sandbox [1].
Overall
I’m glad to see that an ecosystem of relying parties has sprouted up around Twitter. It’s convenient, and it makes sense. I know that it aggregates some risk into my Twitter account, but I still feel that’s better than trying to manage a separate username and password for every web site.
Next instalment… Google.
Update 21 Sep 2010 – you can review the apps connected to your Twitter account in the settings/connections page
[1] Some experimentation with incognito windows on Chrome seems to indicate that you get a single cookie sandbox away from the main Chrome instance, so you can’t just open up fresh windows for each identity :(
Filed under: identity | Leave a Comment
Tags: federated, federation, identity, oauth, OpenID, PeerIndex, persona, PlanCa.st, twitter

No Responses Yet to “Identity Providers – Twitter”