Using Amazon EC2 as a web proxy
I’ve been meaning to try this out for some time, and my recent trials with Amazon’s US Kindle Store prodded me into action.
The theory
Popular SSH clients (like OpenSSH and Putty) have features that allow tunneling. Amazon Machine Images (AMIs) normally have some way of being administered over SSH. So… start up an EC2 instance where you want a tunnel end point (in my case the US) SSH into it, and let some web traffic hitch a ride.
The practice
Finding an AMI
There are LOTS of AMIs out there, and the requirement for this is nothing more than an SSH daemon. For the purpose of my test I used one of my old AMIs that I made with CohesiveFT Elastic Server.
Make sure that SSH ports are open
The security group that you will start your machine in should be reachable on port 22 from your IP. This can be set in the AWS console or using ec2-auth:
ec2auth securitygroup -P tcp -p 22 -s your_physical_machine_IP/32
Start your AMI
From the AWS console or EC2 API Tools (or whatever your preferred higher level tool is).
SSH into your EC2 instance
For this you will need an instance name (like ec2-50-16-32-41.compute-1.amazonaws.com) or its IP (50.16.32.41) a username and password (and in some cases you may also need a correctly configured private key). There are two methods that I’ll illustrate (and I’ll use 9999 as the proxy port, but you could use anything – 8000, 8080 and 8888 are other popular choices)
Using OpenSSH
On Windows you’ll need Cygwin to get OpenSSH. On most Linux distros it should be there already.
ssh -D 9999 username@instance_name
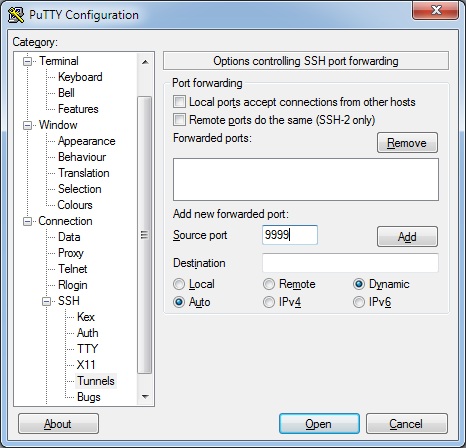
Using Putty
Put the instance name in:
Then add an SSH Tunnel before clicking Open:
Once you sign in you should have a working tunnel, now to use it.
Configuring Firefox to use the tunnel
I use Chrome as my main browser, and tend to use Firefox for experimental stuff like this.
To set a proxy select Tools -> Options then Advanced, Network, Settings:
Once there you want to select Manual proxy configuration and define a SOCKS Host of localhost:9999 with No Proxy for localhost, 127.0.0.1:
That’s it :)
When you OK back to the browser you should now be connected to the web via the EC2 instance. Don’t forget to shut it down when you’re done and revert Firefox back to ‘No proxy‘.
NB I’ve read that sites within the Amazon cloud (like the AWS site itself) may not behave as expected when your source IP is within EC2. I can say for sure that it works fine with the Amazon Kindle store (though as soon as I sign in I get pointed back to the .co.uk site)
NB2 I’m well aware that there are other means/services for doing this. EC2 is probably optimal for short term low bandwidth usage. Other approaches (see below) may be better if you want to move a lot of material around over a longer period of time.
Todo
This is fine for browsing and other stuff that lets you define a SOCKS proxy. There are circumstances where that’s not enough, and I’ll post some other day on how something like OpenVPN might be used to do this (or you could read @samj’s version)
Updates
Update 1 – 13 Dec 2010 – I got sick of fiddling with Proxy settings in Firefox, so I’ve now started using Wyzo for all of my proxied browsing. It’s pretty much a skinned Firefox, so the user experience is the same, but it saves me much clicking.
Update 2 – 14 Dec 2010 – Wyzo set of my anti malware software (I use Prevx). I’m pretty certain that it’s a false positive, but when you list out the things that a browser does to a machine it looks pretty evil (and I am disappointed that it made itself default browser without asking – that’s just rude, but also easy to fix):
WYZO.EXE has been seen to perform the following behavior:
- The Process is packed and/or encrypted using a software packing process
- This Process Deletes Other Processes From Disk
- Can communicate with other computer systems using HTTP protocols
- Executes a ProcessCreates a TCP port which listens and is available for communication initiated by other computers
- Registers a Dynamic Link Library FileThis process creates other processes on disk
- Can make outbound communication to other computers, IM chat rooms and other services using IRC protocols
- Communicates with other computers using FTP connections
- Executes Processes stored in Temporary Folders
- Adds products to the system registry
- Writes to another Process’s Virtual Memory (Process Hijacking)
- Adds an ActiveX component changing or modifying the function of your browser
- Deletes an ActiveX componentWYZO.EXE has been the subject of the following behavior:
- Created as a process on disk
- Executed as a Process
- Terminated as a ProcessHas code inserted into its Virtual Memory space by other programs
- Deleted as a process from disk
- Executed by Internet Explorer
- Changes to the file command map within the registry
Update 3 – 14 Dec 2010 – I should also mention that I’ve had issues with PeerBlock getting in the way of connections to EC2. For some reason somebody involved in maintaining the IP blacklist has decided that one of the Amazon ranges is ev1L. Now that I’m aware of the issue it’s simple to put an exception in place and restart my Putty session.
Update 4 – 30 Jun 2011 – After a few machine rebuilds and the discovery of FireFox profiles I’ve stopped using Wyzo. I’ve used ‘firefox.exe -ProfileManager’ to create a new profile called Proxy, and then set that profile up to use my proxy. Then I created a shortcut to FireFox with ‘-p Proxy’ appended (and pinned it to the taskbar).
Filed under: cloud, howto | 18 Comments
Tags: amazon, AMI, ec2, howto, OpenSSH, proxy, Putty, SOCKS, SSH, web



I do something similar to access US only websites however using squid proxy as well, not just a ssh tunnel.
Search the net plenty of people have expanded this basic idea to include vpn access etc.
Have Fun
The first article I found on using EC2 as a proxy also mentioned squid, though it wasn’t really clear to me what it brought to the party other than additional complexity.
Lots of additional comments on this over at Hacker News.
After a bit more research and experimentation I’ve had this working using an EC2 micro instance. I was initially a bit scared of by the EBS requirement for t1.micro, but that’s just because I didn’t understand it properly. EBS goes away when an instance is terminated, so the premium for the storage is minimal (if you left the lights on all month then the micro instance costs $14.40 and the EBS for a default 15GB drive would add another $1.50).
Using the Ubuntu images I just need the command line:
ec2-run-instances ami-480df921 –instance-type t1.micro –region us-east-1 –key MyKeyName
I thought that Amazon was now giving away micro images.
fwiw, I use a similar proxying approach to get BBC channels out of UK, although I’m having to use my own physical computer – it’s a 15 year old 90MHz Pentium box and is fine for video in an airport.
The free micro instances are only for new customers (and I’ve been signed up to AWS since before EC2 even came on the scene).
Proxying back to a home machine can be useful, though bandwidth can be an issue for ADSL users (as the slow uplink becomes a bottleneck). I’ve also been using IaaS machines from other providers in the UK for when I need to pretend that I’m back at/near home.
If you’ve been a customer of Amazon for awhile but have not used EC2, just shoot them an email and they will usually give you a free year still. I had an EC2 account a year ago that i never actually used and they reset the year for me becasue of it. Just a quick FYI.
SSH tunnel suddenly stopped working for me on multiple devices. tcpdump and sshd debug log show nothing. It is as if Amazon is blocking it. Anyone else experiencing this?
No such problems at my end. Most likely issue is firewall (either local or at EC2), so I’d suggest checking config on that.
is there logs of your traffic on the instance?
Not unless you run tcpdump or similar. Of course it’s possible that Amazon keeps (some) logs.